"Phishing is a cybercrime in which a target or targets are contacted by email, telephone or text message by someone posing as a legitimate institution to lure individuals into providing sensitive data such as personally identifiable information, banking, and credit card details, and passwords. The information is then used to access important accounts and can result in identity theft and financial loss." www.phishing.org
How to Detect Common Phishing Attacks
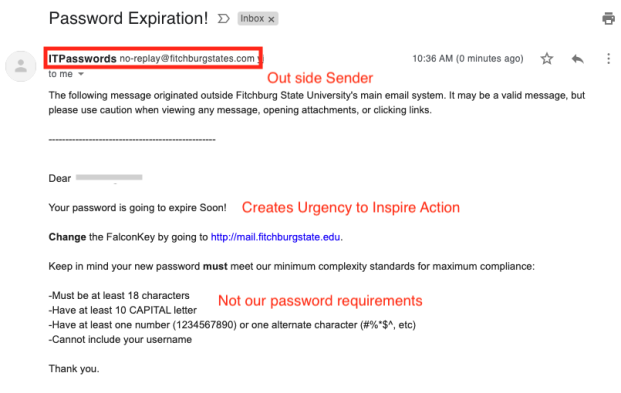
In the following example, the email sender is unrecognized:
no-replay@fitchburgstates.com
The email is trying to create a sense of urgency to inspire action. Wanting you to do something now. Additionally, the email has improper grammar and extraneous requirements for passwords.
The following is an example of the unsecured fake website vs the secured site:
How to Protect Yourself
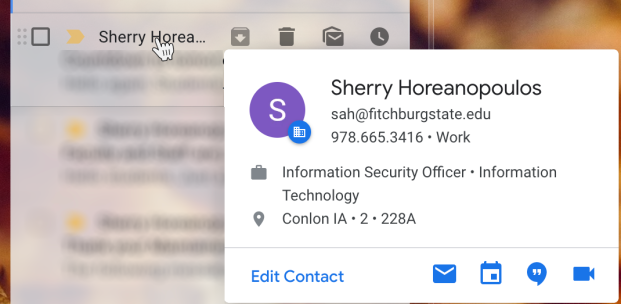
Check the Sender's Email Address
Hover over the sender name to see additional details. Make sure the name and email are legit and the sender is someone you recognize.
Be Cautious of Links Contained in Emails—Think Before You Click!
Hover over the links in an email to see what website address each is pointing to. Do they point to the website they're supposed to? A phishing email may claim to be from a legit site but the links in the email lead elsewhere.
When in doubt, go directly to the website by typing the website address in your browser's address bar rather than clicking a link in the email you received.
Be Wary of Email Attachments
Only open attachments that come from known senders. Attackers want you to open their email attachments—this is one way they try to install malware on your computer. If the attachment wants you to enable macros or content it is likely trying to install something on your computer. Never click/enable macros or content from unknown sources.
What Should I Do if I Receive a Suspicious Email?
Send any suspicious emails to phishtank@fitchburgstate.edu.